|
|
TITLE |
||
|
|
|||
|
DOCUMENT ID |
6111
Appendix T1: Administrative
Control using Locks and Tags Procedure |
||
|
|
|||
This appendix
contains the guidelines for implementing administrative
controls relating to locks and/or tags to restrict equipment operation,
use, or tampering of equipment for reasons other than maintenance, service work,
or construction type work activities. LTT activities that require personal
protection are described in ES&H Manual Chapter 6110
Lock, Tag, Try (LTT) Program.
Note: Management authority may be delegated to a
task-qualified TJNAF employee at the discretion of the responsible manager.
· Current in SAF 104 Lock, Tag, and Try
· Identify yourself
and/or your work group on an applied administrative lock and/or tag; unless
ownership is apparent.
· Remove only
those locks or tags that you apply or have been listed as an authorized
individual.
·
Recognize and respect all administrative lock and tag
control measures.
Unless
otherwise stated only Qualified Individuals may perform the process steps
outlined below.
3.1
Apply Administrative
Locks and Tags
Step 1: Clearly identify the configuration of the equipment or system to be controlled
Do not proceed
until you are certain of all the hazards associated with the operation of the
equipment or system and the proper configuration for control.
|
NOTE: Be alert to
multiple energy sources. |
Step 2:
Notify Others
Appropriately coordinate with all affected groups and/or individuals before locking or tagging the equipment.
Step 3: Configuration Control
Ensure the Qualified Individual’s name (or working group) is
displayed, unless ownership is obvious. Name all individuals or groups
authorized to modify the administrative lock and/or tag.
·
Locks:
o
Are clearly
distinguishable from those used for maintenance, service work, or construction
type work activities. DO NOT USE Jefferson Lab approved Danger LTT Locks.
o
Prevent unauthorized
individuals from inadvertently changing the intended configuration.
o
Multi-lock hasp:
–
if additional
administrative controls are to be applied
– if another LTT device is to be applied later for maintenance, service work, or construction type work activity
DO NOT USE:

·
Tags:
o
Are clearly distinguishable
from those used for maintenance, service work, or construction type work
activities. DO NOT USE Jefferson Lab approved Danger Tags.
o
Affixed so they are
immediately apparent to anyone who might attempt to operate the device.
|
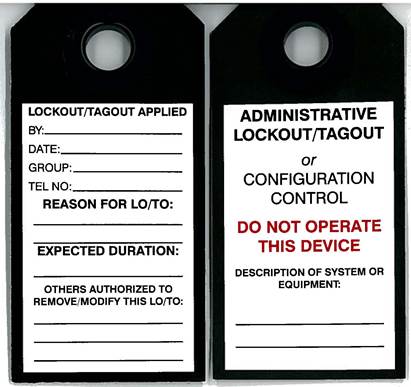
USE: |
DO NOT USE: |
|
Back Front |
|
Step 4: Affix Administrative Lock and/or Tag
·
Place the equipment or
system into the intended state.
· Attach an appropriate administrative lock and/or tag, by durable means to the shackle of the accompanied lock, or a
non-reusable method capable of withstanding a 50-pound pull, minimally
equivalent to a nylon cable tie.
Step 5: Verify Effectiveness
· When appropriate, have an independent qualified individual verify
the effectiveness of the administrative control to ensure the equipment is in
the desired state.
Step 6: Removal of Administrative Locks and/or Tags[1]
·
An authorized individual
notifies all affected parties prior to the action.
· When all affected individuals are ready, an authorized individual
may remove the administrative lock and/or tag.
|
NOTE: The removal
of equipment, that has lock(s) and/or tag(s) attached to it, constitutes a
removal of the lock(s) and/or tag(s); therefore all
lock(s) and/or tag(s) shall be removed by their owners (or anyone listed on
the tag as an authorized individual) before work is performed on the
equipment. |
3.2
Transition
from Administrative
Lock and/or Tag to Danger
LTT
Administrative locks and/or tags securing equipment must be
replaced or augmented with LTT locks/tags during maintenance, service, or
construction type work activity to ensure all energy sources are secure. This
is done in accordance with ES&H Manual Chapter 6110 Lock, Tag, Try
(LTT) Program.
3.3
Special
Administrative
Lock or Tag Removal[2]
Use ES&H
Manual Chapter 6110 Appendix T2
Special Lock and Tag Removal Procedure to remove administrative locks
or tags whose owners cannot be located.
4.0
Revision
Summary
Periodic Review – 01/30/2023 – per CBailey (Industrial Safety Program Lead) change TPOC from TKujawa to BRodriguez; no content changes necessary
Periodic Review – 10/24/20 – No changes per TPOC
Revision
0.4 – 10/24/17 – Periodic Review; updated
Process Step 4 for clarification
Revision
0.3 – 11/03/14 – Periodic Review; no substantive changes per TPOC
Revision 0.2 – 08/02/13
– Added note to Process
Step 6 for clarification of equipment removal
Revision
0.1 – 11/10/11 – Periodic Review; clarification
of process steps
Revision
0.0 – 06/08/09 – Initial
content
|
|
ISSUING AUTHORITY |
TECHNICAL
POINT-OF-CONTACT |
APPROVAL DATE |
REVIEW DATE |
REVIEW CYCLE |
rev |
|
|
|
ES&H Division |
10.24.2017 |
01.30.2023 |
3 years |
0.4 |
|